ransomware what it is and what to do about it
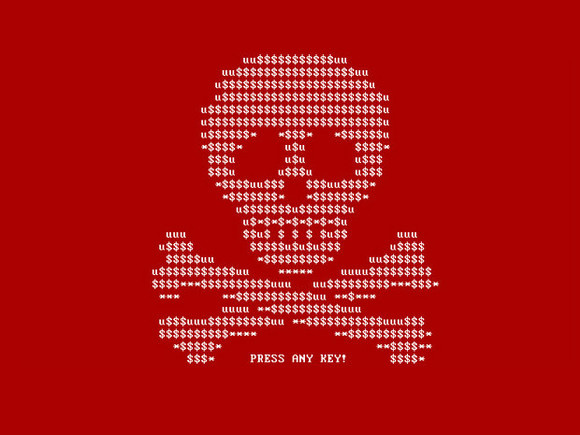
Pic this.
It'south late in the evening. Maybe you opened your laptop to check your email "i final fourth dimension." Only this time, something is incorrect.
It's slow. Files won't open. Yous're getting error messages like "unknown file type" on your Windows machine or, if y'all're a Mac user, "no associated application." Or maybe you're already completely locked out.
And so, the phone rings. It's your Information technology team, and you hear the words you were hoping and praying to the IT gods non to hear, "We've been breached."
You await back down at your laptop, and in that location it is in blackness and white (and usually carmine).
Yous've been infected with ransomware. You have lots of visitor.
This post was originally published during April of 2019 and updated in October of 2020. Sadly, ransomware has only become more prevalent since so. We've updated the post to reflect the current state of ransomware and to help individuals and businesses protect their information.
In 2020, the FBI's Internet Crime Complaint Eye received 2,474 ransomware complaints, and those are just the ones that got reported. Cybersecurity Ventures expects that businesses will fall victim to a ransomware set on every 11 seconds in 2021, up from every xiv seconds in 2019, and every forty seconds in 2016.
Ransomware attacks are on the ascension and have been getting more than unsafe in recent years. An attack on corporate networks that encrypts sensitive information can cost businesses hundreds of thousands or even millions of dollars. In 2020, the total number of global ransomware reports increased by 485% twelvemonth-over-year according to the latest Threat Landscape Report 2020 past Bitdefender.
Compounding the trend, more than people are working remotely as the global pandemic continues to change business environments, and cybercriminals capitalize on the opportunity to assault users working outside the corporate firewall. An uptick in scams and phishing attempts across all platforms indicated that attackers leveraged bug related to COVID-19 to exploit fear and misinformation. Bitdefender noted attacks focused on COVID-19 related messaging in the first one-half of 2020 before shifting to impersonations of cyberbanking, delivery, and travel services in the second one-half.
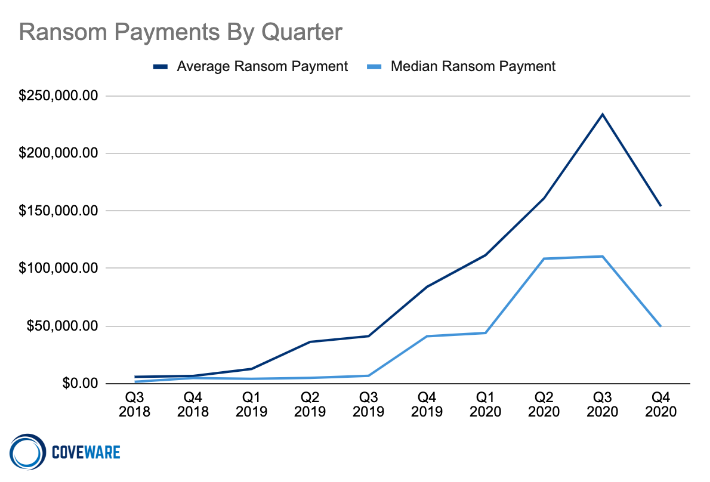
Ransom amounts are also reaching new heights. Attempts have gone as high as $50 million—the largest attempted ransom ever. The astronomical demands had many companies saying "enough is enough" and refusing to make payments toward the end of 2020. Coveware's Q4 2020 Quarterly Ransomware Report noted that boilerplate payments decreased 34% to $154,108 from $233,817 in Q3 of 2020. They aspect the decrease to eroding trust that hackers volition actually delete sensitive information, with many reports of information beingness released to the public after payments are made.
Ransomware affects all industries, from tech to healthcare, and oil and gas to college education. Even during a global pandemic, in Q4 of 2020, co-ordinate to Coveware, the healthcare sector was the nearly common industry targeted by ransomware followed past professional services and the public sector. And so if there's any expectation that a business concern' mission or service to the world might deter malicious actors, that'due south an assumption to leave in the past.
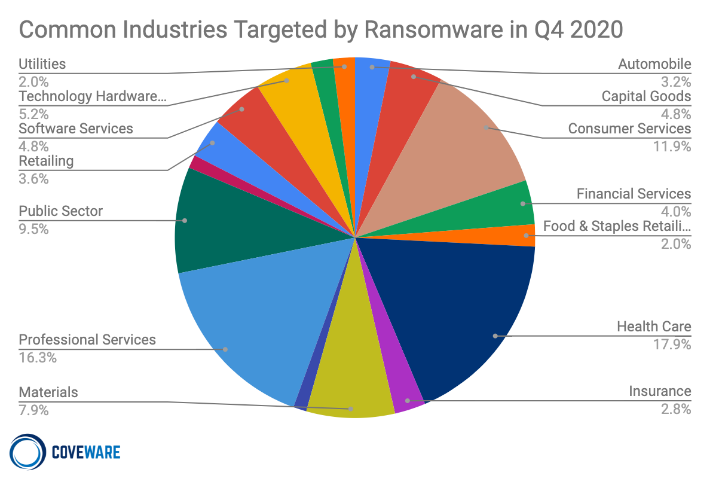
Ransomware continues to be a major threat to businesses in all sectors, with some areas getting hit particularly hard, specially teaching and healthcare. In 2020, one,681 schools were affected by ransomware besides as 560 healthcare facilities according to a report from Emsisoft, a security solutions provider.
In March of 2021, attackers demanded an astronomical $40 million from Broward County Public Schools, the nation's sixth largest schoolhouse commune. In August and September of 2020, 57% of ransomware attacks reported to the federal Multi-State Information Sharing and Assay Center involved schools, compared to 28% of all reported ransomware incidents from January through July.
The instruction sector makes an easy marking for hackers, especially this past yr—schools with strapped budgets and aging It equipment entered an unprecedented year of IT-reliant remote teaching. Schools as well store sensitive pupil information they're vested in protecting, making them more likely to pay ransoms rather than have their data published.
In healthcare, since 2016, 270 ransomware attacks targeted two,100 clinics, hospitals, and other wellness-related businesses, with an estimated overall price of $31 million.
Attacks on healthcare and the public sector cause life-threatening challenges. "The fact that there were no ransomware-related deaths in the U.S. last year was simply due to good luck," Emsisoft CTO, Fabian Wosar said in the written report. "Security needs to be bolstered across the public sector before that luck runs out and lives are lost."
The commencement step in bolstering security is understanding how ransomware works and how you lot can protect your business concern or organization from an attack. Read on to learn how to protect yourself from ransomware.
How Does Ransomware Work?
Ransomware typically spreads via spam, phishing emails, or through social engineering efforts. It likewise can exist spread through websites or bulldoze-by downloads to infect an endpoint and penetrate the network. Infection methods are constantly evolving and there are countless ways 1'southward technology can go infected (see section six, "How to Prevent a Ransomware Attack"). Once in place, the ransomware then locks all files it tin can admission using stiff encryption. Finally, the malware demands a ransom (typically payable in Bitcoin) to decrypt the files and restore full operations to the affected IT systems.
Encrypting ransomware or cryptoware is by far the most common recent variety of ransomware. Other types that might be encountered are:
- Not-encrypting ransomware or lock screens (restricts admission to files and data, but does non encrypt them).
- Ransomware that encrypts the Master Boot Record (MBR) of a drive or Microsoft's NTFS, which prevents victims' computers from being booted up in a alive OS surroundings.
- Leakware or extortionware (steals compromising or damaging data that the attackers and so threaten to release if bribe is not paid).
- Mobile device ransomware (infects cell-phones through drive-by downloads or imitation apps).
Latest Trends in Malware:
Over the by year, social distancing has caused people to work, store, and acquire from dwelling house in means that no 1 could have imagined. With this increase in online activity comes more online security risks, with targets centered on government and healthcare organizations. Fifty-fifty though these institutions are essential during a pandemic, cyber criminals aren't deterred. They continue to evolve their strategy and method of attack, concentrating on areas that provide the highest payback for the to the lowest degree effort.
Today, with the emergence of ransomware as a service (RaaS), cybercriminals don't even need to be very savvy to pull off an attack. They can shop for affiliate software on the dark web where the developer gets a cut of the take. Oleg Skulkin, Atomic number 82 Digital Forensics Specialist at Group-IB, a cybersecurity house, shared with ZDNet that, "Affiliate programs brand this kind of attack more attractive for cybercriminals. The tremendous popularity of such attacks made almost every company, regardless of their size and industry, a potential victim."
The question shouldn't be, "When will the next ransomware assail occur?" but rather, "Has there already been a alienation today?" With no indication that ransomware attacks are slowing, it's better to exist overly prepared when information technology comes to Information technology security, and the importance of being backed upwards and secure should be mutual practice for organizations both big and small.
Steps in a Typical Ransomware Assail
The typical steps in a ransomware set on are:
-
-
- 1. Infection: After information technology has been delivered to the arrangement via email attachment, phishing email, infected application or other method, the ransomware installs itself on the endpoint and any network devices it tin access.
-
- two. Secure Key Commutation: The ransomware contacts the control and control server operated by the cybercriminals backside the attack to generate the cryptographic keys to be used on the local system.
-
- 3. Encryption: The ransomware starts encrypting whatever files it tin notice on local machines and the network.
-
- four. Extortion: With the encryption work done, the ransomware displays instructions for extortion and bribe payment, threatening destruction of data if payment is not fabricated.
-
-
- 5. Unlocking: Organizations tin can either pay the bribe and promise for the cybercriminals to really decrypt the affected files, or they can attempt recovery by removing infected files and systems from the network and restoring information from make clean backups. Unfortunately, negotiating with cyber criminals is often a lost cause as a recent study found that
42% of organizations
- who paid a ransom did not get their files decrypted.
-
Who Gets Attacked?
Ransomware attacks target firms of all sizes—5% or more of businesses in the top x industry sectors take been attacked—and no size business, from small and medium-sized businesses to enterprises, is immune. Attacks are on the rising in every sector and in every size of business.
Also, the phishing endeavour that targeted the Globe Wellness System (WHO), though unsuccessful, proves that attackers bear witness no sense of "out of bounds" targets when it comes to choosing their victims. These attempts indicate that organizations which oftentimes have weaker controls and out-of-engagement or unsophisticated IT systems should take extra caution to protect themselves and their information.
The U.S. ranks the highest in the number of ransomware attacks, followed by Germany and then French republic. Windows computers are the main targets, just ransomware strains exist for Macintosh and Linux, as well.
The unfortunate truth is that ransomware has become so widespread that for most companies information technology is a certainty that they will exist exposed to some degree to a ransomware or malware attack. The best they can do is to be prepared and understand the best means to minimize the impact of ransomware.
"Ransomware is more about manipulating vulnerabilities in homo psychology than the antagonist'southward technological sophistication."—James Scott, Institute for Critical Infrastructure Applied science
Phishing emails, malicious email attachments, and visiting compromised websites have been common vehicles of infection (we wrote about phishing in "Summit 10 Means to Protect Yourself Against Phishing Attacks"), but other methods have become more common recently. Weaknesses in Microsoft's Server Message Cake (SMB) and Remote Desktop Protocol (RDP) have immune cryptoworms to spread. Desktop applications—in one case an accounting bundle—and even Microsoft Role (Microsoft's Dynamic Data Exchange (DDE)) accept likewise been the agents of infection.
Recent ransomware strains such equally Petya, CryptoLocker, and WannaCry have incorporated worms to spread themselves beyond networks, earning the nickname, "cryptoworms."
How to Defeat Ransomware
So, you've been attacked by ransomware. What should you practise adjacent?
-
- 1. Isolate the Infection: Preclude the infection from spreading by separating all infected computers from each other, shared storage, and the network.
-
- two. Identify the Infection: From letters, bear witness on the reckoner, and identification tools, determine which malware strain y'all are dealing with.
-
- 3. Report: Study to the authorities to back up and coordinate measures to counter assault.
-
- four. Decide Your Options: You take a number of ways to deal with the infection. Determine which arroyo is best for you.
-
- five. Restore and Refresh: Use rubber backups and program and software sources to restore your computer or outfit a new platform.
-
- 6. Plan to Prevent Recurrence: Make an assessment of how the infection occurred and what you can do to put measures into identify that will prevent it from happening again.
1. Isolate the Infection
The rate and speed of ransomware detection is critical in combating fast moving attacks before they succeed in spreading beyond networks and encrypting vital data.
The first matter to do when a computer is suspected of being infected is to isolate it from other computers and storage devices. Disconnect it from the network (both wired and Wi-Fi) and from whatsoever external storage devices. Cryptoworms actively seek out connections and other computers, so you desire to prevent that happening. Y'all also don't want the ransomware communicating across the network with its command and control center.
Be enlightened that in that location may be more than just 1 patient zero, meaning that the ransomware may have entered your organisation or abode through multiple computers, or may exist dormant and not yet shown itself on some systems. Treat all connected and networked computers with suspicion and utilise measures to ensure that all systems are not infected.
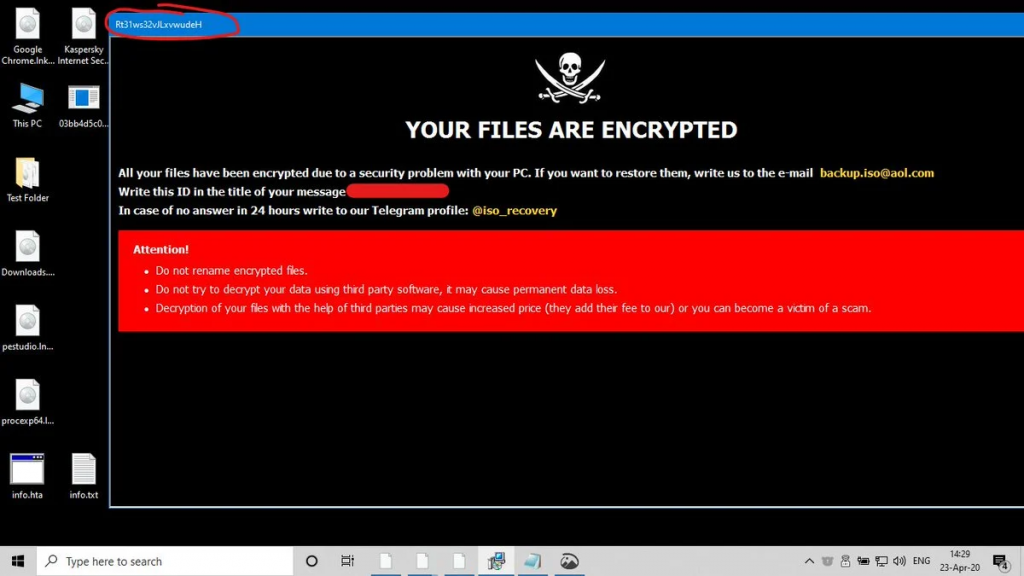
two. Identify the Infection
Nigh ofttimes the ransomware will identify itself when it asks for ransom. There are numerous sites that aid you identify ransomware, including ID Ransomware. The No More than Ransom! Project provides the Crypto Sheriff to assistance identify ransomware.
Identifying the ransomware will help yous understand what blazon of ransomware you have, how it propagates, what types of files it encrypts, and maybe what your options are for removal and disinfection. It besides volition enable you to report the attack to the authorities, which is recommended.
iii. Report to the Authorities
You'll exist doing everyone a favor past reporting all ransomware attacks to the authorities. The FBI urges ransomware victims to report ransomware incidents regardless of the outcome. Victim reporting provides law enforcement with a greater understanding of the threat, provides justification for ransomware investigations, and contributes relevant information to ongoing ransomware cases. Knowing more about victims and their experiences with ransomware will help the FBI to determine who is behind the attacks and how they are identifying or targeting victims.
You tin file a study with the FBI at the Internet Law-breaking Complaint Eye.
There are other ways to report ransomware, equally well.
iv. Determine Your Options
Your options when infected with ransomware are:
- To pay the ransom.
- To attempt to remove the malware.
- To wipe the system(s) and reinstall from scratch.
Information technology'due south generally considered a bad idea to pay the bribe. Paying the ransom encourages more ransomware, and in many cases the unlocking of the encrypted files is not successful.
In a recent survey, more than than three-quarters of respondents said their organization is not at all likely to pay the ransom in order to recover their information (77%). Only a minor minority said they were willing to pay some ransom (3% of companies have already ready a Bitcoin account in preparation).
Even if you lot determine to pay, information technology'south very possible you won't get back your data.
That leaves ii other options: removing the malware and selectively restoring your arrangement, or wiping everything and installing from scratch.
v. Restore or Start Fresh
You have the choice of trying to remove the malware from your systems or wiping your systems and reinstalling from condom backups and clean Bone and awarding sources.
Get Rid of the Infection
There are cyberspace sites and software packages that merits to be able to remove ransomware from systems. The No More Bribe! Project is one. Other options can be constitute, as well.
Whether you can successfully and completely remove an infection is up for argue. A working decryptor doesn't exist for every known ransomware, and unfortunately information technology'southward true that the newer the ransomware, the more sophisticated information technology's likely to be and the less time the practiced guys have had to develop a decryptor.
Information technology'south Best to Wipe All Systems Completely
The surest fashion of existence certain that malware or ransomware has been removed from a arrangement is to do a complete wipe of all storage devices and reinstall everything from scratch. Formatting the hard disks in your system will ensure that no remnants of the malware remain.
If yous've been post-obit a sound backup strategy, y'all should accept copies of all your documents, media, and of import files right up to the time of the infection.
Exist sure to make up one's mind the appointment of infection every bit well as you lot can from malware file dates, messages, and other information you take uncovered about how your detail malware operates. Consider that an infection might have been dormant in your organization for a while earlier information technology activated and made significant changes to your system. Identifying and learning almost the particular malware that attacked your systems will enable you to understand how that malware functions and what your best strategy should be for restoring your systems.
Select a backup or backups that were made prior to the engagement of the initial ransomware infection. With Extended Version History, you tin can go dorsum in time and specify the date prior to which y'all wish to restore files.
If you lot've been following a good backup policy with both local and off-site backups, you should be able to use backup copies that yous are sure were not connected to your network after the time of assail and hence protected from infection. Backup drives that were completely asunder should be safe, as are files stored in the cloud.
System Restores Are Not the Best Strategy for Dealing With Ransomware and Malware
You might be tempted to utilise a Arrangement Restore point to get your system back up and running. Organisation Restore is non a proficient solution for removing viruses or other malware. Since malicious software is typically buried inside all kinds of places on a system, yous can't rely on System Restore being able to root out all parts of the malware. Too, Arrangement Restore does not save old copies of your personal files as part of its snapshot. Information technology besides volition not delete or replace any of your personal files when you perform a restoration, so don't count on System Restore equally working like a backup. You should ever have a good backup procedure in identify for all your personal files.
Local backups can too exist encrypted by ransomware. If your fill-in solution is local and connected to a computer that gets hit with ransomware, the chances are good your backups will be encrypted along with the remainder of your data.
With a practiced backup solution that is isolated from your local computers, y'all can easily obtain the files you need to get your arrangement working once more. You accept the flexibility to decide which files to restore, from which appointment you desire to restore, and how to obtain the files you demand to restore your organization.
You'll need to reinstall your Bone and software applications from the source media or the internet. If yous've been managing your account and software credentials in a sound manner, you should exist able to reactivate accounts for applications that crave it. If you use a password manager to store your business relationship numbers, usernames, passwords, and other essential information, y'all tin access that data through their web interface or mobile applications. You just need to be sure that you still know your master username and password to obtain admission to these programs.

half dozen. How to Prevent a Ransomware Attack
"Ransomware is at an unprecedented level and requires international investigation."—European police agency EuroPol
A ransomware attack tin can be devastating for a home or a concern. Valuable and irreplaceable files can be lost and tens or fifty-fifty hundreds of hours of attempt can be required to go rid of the infection and become systems working once again.
Ransomware attacks continue to evolve and set on methods get more sophisticated all the time. Y'all don't have to be office of the statistics. With practiced planning and smart practices, you lot can prevent ransomware from affecting your systems.
Know How Viruses Enter Your Workplace and Computer
To be prepared, you need to know how ransomware tin can enter your system. These methods of gaining access to your systems are known equally attack vectors.
Assault vectors can be divided into ii types: human attack vectors and machine attack vectors.
Homo Attack Vectors
Often, viruses need the assistance of humans to enter computers then they use what's known as social engineering. In the context of data security, social engineering is the use of deception to dispense individuals into divulging confidential or personal data that may exist used for fraudulent purposes. In other words, people can be fooled into giving up data that they otherwise would not divulge.
Common human assail vectors include:
1. Phishing
Phishing uses fake emails to trick people into clicking on a link or opening an attachment that carries a malware payload. The email might exist sent to one person or many within an organization. Sometimes the emails are targeted to brand them seem more than credible. The attackers have the fourth dimension to enquiry the individual targets and businesses so their e-mail appears legitimate. The sender might exist faked to be someone known to the recipient or the subject matter relevant to the recipient'southward job. When personalized in this manner, the technique is known equally spear phishing. Read more virtually this blazon of attack vector in our post, "Top 10 Ways to Protect Yourself Against Phishing Attacks."
2. SMSishing
SMSishing uses text messages to get recipients to navigate to a site or enter personal data on their device. Mutual approaches utilize authentication messages or messages that announced to be from a financial or other service provider. Some SMSishing ransomware attempt to propagate themselves by sending themselves to all contacts in the device's contacts list.
3. Vishing
In a similar manner to email and SMS, vishing uses voicemail to deceive the victim. The voicemail recipient is instructed to call a number that is often spoofed to appear legitimate. If the victim calls the number, they are taken through a series of actions to right some made-up trouble. The instructions include having the victim install malware on their calculator. Cybercriminals can appear professional and use sound furnishings and other means to announced legitimate. Like spear phishing, vishing tin be targeted to an individual or company using information that the cybercriminals accept collected.
4. Social Media
Social media can be a powerful vehicle to convince a victim to open a downloaded image from a social media site or have some other compromising action. The carrier might be music, video, or other active content that one time opened infects the user's system.
5. Instant Messaging
Instant messaging clients tin can be hacked past cybercriminals and used to distribute malware to the victim'south contact list. This technique was 1 of the methods used to distribute the Locky ransomware to unsuspecting recipients.
Machine Attack Vectors
The other type of assail vector is car to machine. Humans are involved to some extent as they might facilitate the assail by visiting a website or using a estimator, but the attack procedure is automatic and doesn't crave any explicit human cooperation to invade your figurer or network.
i. Drive-by
Drive-by has this moniker because all it takes for the victim to become infected is to open a webpage with malicious code in an image or active content.
two. System Vulnerabilities
Cybercriminals learn the vulnerabilities of specific systems and exploit those vulnerabilities to break in and install ransomware on the automobile. This virtually often happens to systems that are not patched with the latest security releases.
3. Malvertising
Malvertising is like drive-by, but uses ads to deliver malware. These ads might be placed on search engines or pop social media sites in society to reach a large audience. A mutual host for malvertising is adults-only sites.
4. Network Propagation
However a piece of ransomware enters a system, one time information technology has, it tin can scan for file shares and accessible computers and spread itself beyond the network or shared system. Companies without adequate security might have their company file server and other network shares infected equally well. From there, the malware will spread as far every bit it can until it runs out of attainable systems or meets security barriers.
5. Propagation Through Shared Services
Online services such equally file sharing or syncing services can be used to propagate ransomware. If the ransomware ends up in a shared binder on a home machine, the infection tin be transferred to an role or to other connected machines. If the service is ready to automatically sync when files are added or changed, every bit many file sharing services are, then a malicious virus can be widely propagated in only milliseconds.
Information technology'due south important to be careful and consider the settings you use for systems that automatically sync, and to be cautious about sharing files with others unless you know exactly where they came from.

Best Practices to Defeat Ransomware
Security experts propose several precautionary measures for preventing a ransomware attack.
-
-
- one. Use anti-virus and anti-malware software or other security policies to block known payloads from launching.
-
- two. Make frequent, comprehensive backups of all of import files and isolate them from local and open networks.
-
- 3. Immutable backup options such as Object Lock offer users a manner to maintain truly air-gapped backups. The data is fixed, unchangeable, and cannot be deleted within the time frame set up past the end-user. With immutability attack critical data, you can quickly restore uninfected information from your immutable backups, deploy them, and return to business organization without interruption.
-
Object Lock functionality for backups allows you to store objects using a Write One time, Read Many (WORM) model, meaning later it's written, data cannot exist modified. Using Object Lock, no one tin encrypt, tamper with, or delete your protected data for a specified period of time, creating a solid line of defense force against ransomware attacks.
-
- iv. Keep offline backups of data stored in locations inaccessible from any potentially infected estimator, such equally asunder external storage drives or the deject, which prevents them from being accessed past the ransomware.
-
- 5. Install the latest security updates issued past software vendors of your OS and applications. Remember to patch early and patch oft to close known vulnerabilities in operating systems, browsers, and web plugins.
-
- 6. Consider deploying security software to protect endpoints, e-mail servers, and network systems from infection.
-
- 7. Exercise cyber hygiene, such as using caution when opening email attachments and links.
-
- 8. Segment your networks to keep critical computers isolated and to preclude the spread of malware in instance of assail. Turn off unneeded network shares.
-
- 9. Turn off admin rights for users who don't require them. Requite users the lowest system permissions they need to practice their work.
-
- ten. Restrict write permissions on file servers equally much equally possible.
-
- 11. Educate yourself, your employees, and your family unit in best practices to keep malware out of your systems. Update everyone on the latest electronic mail phishing scams and homo engineering aimed at turning victims into abettors.

It's clear that the best fashion to respond to a ransomware attack is to avoid having one in the first place. Other than that, making certain your valuable data is backed up and unreachable by a ransomware infection will ensure that your reanimation and information loss will be minimal or none if yous ever endure an attack.Have you endured a ransomware attack or accept a strategy to avoid becoming a victim? Delight let united states know in the comments.
-
Source: https://www.backblaze.com/blog/complete-guide-ransomware/
0 Response to "ransomware what it is and what to do about it"
Post a Comment